
Simple Guide to Follow for Better Endpoint Protection
Endpoints make up much of a company’s network and IT infrastructure. This is a collection of computers, mobile devices, servers, and smart gadgets. As well

Endpoints make up much of a company’s network and IT infrastructure. This is a collection of computers, mobile devices, servers, and smart gadgets. As well

One of the most difficult types of attacks to detect are those performed by insiders. An “insider” would be anyone that has legitimate access to

Digital footprints cover today’s modern workplace. Employees begin making these the moment they’re hired. They get a company email address and application logins. They may

The holiday shopping season is taking off. This means that scammers have also revved up their engines. They’re primed and ready to take advantage of

When you hear about Microsoft adding security apps to M365, it’s often the business versions. But the pandemic has changed the way that we see

Phishing. It seems you can’t read an article on cybersecurity without it coming up. That’s because phishing is still the number one delivery vehicle for

Few things invoke instant panic like a missing smartphone or laptop. These devices hold a good part of our lives. This includes files, personal financials,
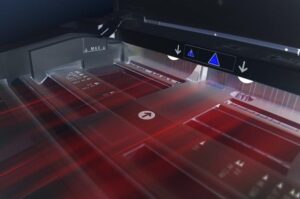
Printing devices are often overlooked when it comes to security. But the reality is, cybercriminals can hack your printer to get confidential information. Your printer

Your data is pivotal to running a successful company. If you don’t have proper security measures in place, hackers can easily steal your data and

Your business can benefit a lot from working with an IT provider. However, you need to avoid several key mistakes when choosing your team. Time
Virtual IT Managed Services | Cybersecurity Services & IT Support Melbourne, AU
S6, Level 2, 64 Victor Crescent
Narre Warren, Victoria 3805
Phone: 03 8903 2570
Email: sales@vitms.com.au
© Copyright 2024 Virtual IT Managed Services Pty Ltd. All rights reserved.